The “Highlights” — To Russia, With Crypto

The Financial Crimes Enforcement Network (“FinCEN”) issued on November 1 a Financial Trend Analysis regarding ransomware-related Bank Secrecy Act (“BSA”) filings during the second half of 2021 (the “Report”). This publication follows up on a similar ransomware trend analysis issued by FinCEN regarding the first half of 2021, on which we blogged here.
In the most recent analysis, FinCEN found that both the number of ransomware-related Suspicious Activity Reports (“SAR”) filed, and the dollar amounts at issue, nearly tripled from 2020 to 2021. The notable takeaways from the Report include:
- Ransomware-related SARs were the highest ever in 2021 (both in number of SARs and in dollar amounts of activity reported).
- Ransomware-related SARs reported amounts totaling almost $1.2 billion in 2021.
- Approximately 75% of ransomware-related incidents between June 2021 and December 2021 were connected to Russia-related ransomware variants.
The Report, which stated that the majority of these ransomware payments were made in Bitcoin, serves as a particular reminder to cryptocurrency exchanges of their role in both identifying and reporting ransomware-related transactions facilitated through their platforms. The Report stresses that SAR filings play an essential role in helping FinCEN identify ransomware trends.
Ransomware Trends and SAR Data
Ransomware is malicious software that encrypts a victim’s files and holds the data hostage until a ransom is paid, generally in cryptocurrency like Bitcoin. Over the past two years, FinCEN has noted a shift in ransomware strategy from high-volume, opportunistic attacks to more selective ransomware attacks, targeting larger enterprises and bigger payouts. This included an increase in “double extortion” tactics, in which ransomware operators not only hold the victim’s data hostage, but also threaten to publish the stolen data if ransom demands are not met. FinCEN also noted that the ransomware “business model” has expanded to include Ransomware-as-a-Service (“Raas”), in which ransomware creators sell user-friendly ransomware kits on the dark web in exchange for a percentage of the ransom.
FinCEN observed a staggering increase in the number and monetary amount of ransomware-related SAR filings in 2021. In 2020, 487 ransomware-related SARs were filed, totaling nearly $416 million. In 2021, 1,489 ransomware-related SARs were filed, totaling nearly $1.2 billion. On average, there were 132 ransomware-related incidents per month in the second half of 2021. This increase in filings may have resulted from FinCEN’s and Treasury’s Office of Foreign Assets Control’s (“OFAC”) Fall 2021 advisories promoting reporting of ransomware-related incidents (here, here, and here). As we have blogged, OFAC has indicated that it may impose civil penalties for sanctions violations resulting from ransomware payments based on strict liability – i.e., a company can be held liable even if it did not know or have reason to know that it was engaging in a transaction that was prohibited by OFAC – even if OFAC states that it applies a self-imposed presumption of non-enforcement that it still may disregard in any particular case.
To highlight the upward trend in ransomware-related SARs, FinCEN provided the following graphs charting (1) the increase in filings, and (2) the increase in dollar value:

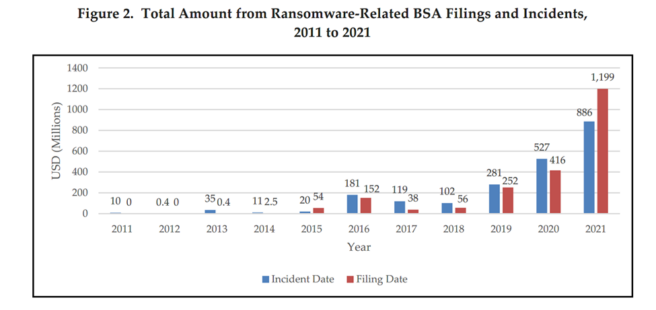
According to FinCEN, the “[f]iling date data is slightly higher than incident date data in Figures 1 and 2 because filing date data can include ransomware events that occurred outside the timeframe covered by the report. Filing date reflects both detection and compliance, where incident date reflects the actual date of payments or demanded payments associated with ransomware events.”
Although the above figures are attention-grabbing, they of course represent incidents reported in filed SARs – which begs the question of how many incidents are not being identified and reported.
Uptick in Russia-Related Ransomware Variants
FinCEN reported than in the second half of 2021 alone, roughly 75% of ransomware-related SARs, and 69% of ransomware incident value, were connected to Russia-related ransomware variants. Although it is difficult to attribute malware, these variants were identified as using Russian-language code, being specifically coded not to attack Russia or post-Soviet states, or as advertising primarily on Russian-language sites. Combined, the top five Russia-related ransomware variants were connected to 376 ransomware incidents, totaling $219.5 million.
Role of Cryptocurrency Exchanges Facilitating Ransomware Payments
In its November 8, 2021 Advisory on Ransomware and the Use of the Financial System to Facilitate Ransomware Payments, FinCEN outlined the typical flow of funds in a ransomware attack, highlighting the role that financial institutions, including money services businesses (“MSB”), play in facilitating these ransom payments. Most ransomware payments involve a victim transmitting funds via wire transfer, ACH transfer, or credit card payment to a convertible virtual currency (“CVC”) exchange, in order to purchase the type and amount of CVC specified by perpetrator. The victim then sends the CVC, often from a virtual wallet hosted by the cryptocurrency exchange, directly to the perpetrator’s designated account or CVC address. The perpetrator then launders the funds to convert them into other CVCs. Cyber insurance companies (“CIC”) and digital forensic incident response companies (“DFIR”) may also play a role in ransomware transactions. CICs may reimburse victim policyholders for remediation services, including hiring DFIRs to negotiate with cybercriminals and facilitate payments.
While ransom payments are most commonly requested in Bitcoin, cybercriminals are increasingly incentivizing victims to pay in Anonymity-Enhanced Cryptocurrencies (“AEC”), such as monero, in order to reduce transparency of financial flows through anonymizing features. Monero recently received a specific “shout out” in the FinCEN enforcement action against Bittrex, which described monero as including “features that prevent tracking by using advanced programming to purposefully insert false information into every transaction on its private blockchain.”
In a November 8, 2021 Advisory on ransomware, FinCEN provided this flowchart highlighting the typical movement of CVC in ransomware attacks:

Ransonware incidents also may trigger OFAC-related restrictions, if payments involve sanctioned persons or jurisdictions. In October 2021, OFAC issued a 28-page sanctions compliance guide for the virtual currency industry, explaining reporting instructions, consequences for non-compliance, and best practices.
Detection, Mitigation, and Reporting
Ransomware continues to pose a significant threat to the U.S. critical infrastructure sectors, businesses, and the public. Financial institutions and MSBs dealing in CVCs play an important role in protecting the U.S. financial system from these types of attacks, through compliance with BSA and OFAC obligations. To detect and mitigate ransomware attacks, FinCEN recommends:
- Incorporating indicators of compromise (“IOC”) from threat data sources into intrusion detection and security alert systems to enable blocking and reporting.
- Contacting law enforcement immediately upon identifying ransomware-related activity, and contacting OFAC where the ransom involves sanctioned payments.
- Reporting suspicious activity to FinCEN by highlighting the presence of “Cyber Event Indicators,” and including IOCs like suspicious email addresses, file names, hashes, domains, and IP addresses on the SAR form.
FinCEN also reminds financial institutions to review the potential “red flag” financial indicators of ransomware in FinCEN’s November 8, 2021 Advisory, which are:
- A financial institution or its customer detects IT enterprise activity that is connected to ransomware cyber indicators or known cyber threat actors. Malicious cyber activity may be evident in system log files, network traffic, or file information.
- When opening a new account or during other interactions with the financial institution, a customer provides information that a payment is in response to a ransomware incident.
- A customer’s CVC address, or an address with which a customer conducts transactions is connected to ransomware variants, payments, or related activity. These connections may appear in open sources or commercial or government analyses.
- An irregular transaction occurs between an organization, especially an organization from a sector at high risk for targeting by ransomware (e.g., government, financial, educational, healthcare) and a DFIR or CIC, especially one known to facilitate ransomware payments.
- A DFIR or CIC customer receives funds from a counterparty and shortly after receipt of funds sends equivalent amounts to a CVC exchange.
- A customer shows limited knowledge of CVC during onboarding or via other interactions with the financial institution, yet inquires about or purchases CVC (particularly if in a large amount or rush requests), which may indicate the customer is a victim of ransomware.
- A customer that has no or limited history of CVC transactions sends a large CVC transaction, particularly when outside a company’s normal business practices.
- A customer that has not identified itself to the CVC exchanger, or registered with FinCEN as a money transmitter, appears to be using the liquidity provided by the exchange to execute large numbers of offsetting transactions between various CVCs, which may indicate that the customer is acting as an unregistered MSB.
- A customer uses a foreign-located CVC exchanger in a high-risk jurisdiction lacking, or known to have inadequate, AML/CFT regulations for CVC entities.
- A customer receives CVC from an external wallet, and immediately initiates multiple, rapid trades among multiple CVCs, especially AECs, with no apparent related purpose, followed by a transaction off the platform. This may be indicative of attempts to break the chain of custody on the respective blockchains or further obfuscate the transaction.
- A customer initiates a transfer of funds involving a mixing service.
- A customer uses an encrypted network (e.g., the onion router) or an unidentified web portal to communicate with the recipient of the CVC transaction.
If you would like to remain updated on these issues, please click here to subscribe to Money Laundering Watch. To learn more about Ballard Spahr’s Anti-Money Laundering Team, please click here.